Associate Microsoft and Pradeo to manage and secure Android Enterprise mobile devices
Want to learn more on how Android Enterprise works with existing mobility management and security solutions? This article will explain how Android Enterprise fits in a standard mobile ecosystem made of Microsoft Endpoint Manager solution and Pradeo Security Mobile Threat Defense.
Android Enterprise arrived like a call to action in the era of mobility. Even though it has its roots in Android 5.0 (Lollipop) launched in 2014, it comes now as a mandatory feature on all Android 10 devices when managed with an Enterprise Mobility Management solution.
Android Enterprise integrates smoothly into Microsoft Endpoint Manager to empower its capabilities and complements with Pradeo Security Mobile Threat Defense to ensure a full real-time protection.
To get a clear understanding on what to expect from Android Enterprise, we will firstly detail its DNA to then extend to its complementariness into the mobile landscape.
The homogenization of management capabilities as Android Enterprise DNA
To interact with devices, Unified Endpoint Management (UEM) solutions used to rely on manufacturers APIs implemented on top of the Android system and bringing a lot of inconsistency from one device to another. To reduce the hassle, Google created a native bundle of APIs enabled for all Android devices, regardless of the manufacturer. This homogenization of management across devices comes along with two key benefits being the creation of a containerized work/personal profile on the device and a managed Google Play store with work-approved applications.
Let’s dive a bit more into the different setup modes of work and personal profiles.
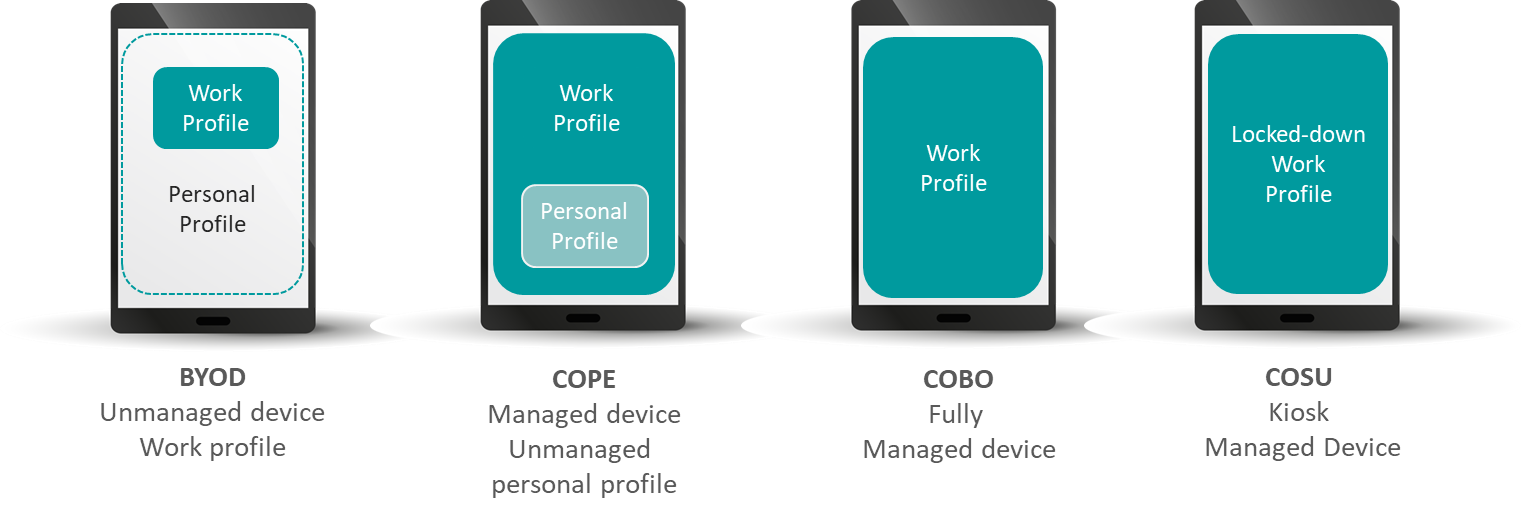
The first mode from left to right called “BYOD” (acronym for Bring Your Own Device) refers to devices personally owned by the collaborators, but which are also used in a corporate context. The core principle in this configuration is that the device is not managed by the company and a containerized area is created for work activities (files, applications…). Therefore, the personal environment masters the device and the company only has control over the work profile.
The second hybrid mode takes the opposing view to BYOD configuration. Here, the work profile masters the whole device and the work/life separation lies in a personal sub-area. This configuration is usually known as COPE standing for Corporate Owned Personally Enabled.
In both COPE and BYOD modes, the separation consists in isolating work/life files, applications, and resources (messages, contacts, call logs…).
The Corporate Owned Business Only (COBO) configuration depicts a device fully managed by the company and strictly aimed for work. Thus, there is no dedicated area for personal activities and the enterprise has a complete view on the device.
Lastly, kiosk-managed devices also referred as COSU (Corporate Owned/Single Use) stick to COBO configuration where the work profile is locked down to only enable a targeted usage.
With these four specific types of configuration, organizations are free to have more or less control over the user device. With an ever-growing BYOD landscape, companies can decide to let employees work on their personal devices, while still having control over the work profile.
Ultimately, this containerization capability, already available in UEMs for some time, simplifies and unifies Android management but doesn’t really add a structuring security piece. At the same time, the managed Google Play store reflects the legacy mobile application management functionality delivered by UEMs.
Therefore, when implementing Microsoft Endpoint Point Manager, administrators will have to determine in which mode they will manage their corporate fleet. To add a layer of security on top of the combo Android Enterprise/Microsoft Endpoint Manager, they will have to pair it with a security layer like Pradeo Security Mobile Threat Defense.
Additional security awareness
Setting up a work/life separation as a data privacy measure adds an extra level of security. This should not be considered as a security gate. The exposure of corporate data through various setup modes needs extra consideration.
Network and device criteria apply for the entire device and a Man-In-The-Middle threat or a root/jailbreak exploit will injure the work profile the same way. Looking at applications, if validating the security level of applications prior to their distribution to the work area is a must-have, the assessment of on-device applications is not to forget. By downloading an application from the store either on the work or personal profile, corporate data are exposed to malware (screen logger, keylogger…) and intrusive or leaky applications (e.g.: exfiltrating contacts…) that could hit from one profile to the other.
In sum, the same security posture requires to be taken to protect Android Enterprise mobile devices as any other device.
Associate Microsoft and Pradeo to manage and secure Android Enterprise mobile devices
Pradeo and Microsoft’s long-lasting partnership aims at bringing security on top of devices management and fully applies in an Android Enterprise environment. The collaboration between the companies covers the two following use cases:
- Agentless application vetting: Pradeo Security solution directly plugs in Microsoft Endpoint Manager (including Microsoft Intune) to retrieve the list of applications installed on the fleet and assess the security level of devices.
- On-device security: the installation of the Pradeo Security agent on devices provides a 360° security coverage and real-time remediation.
Android Enterprise represents a core add-on to the Android framework homogenizing the management of devices across manufacturers and concretizing the undeniable work/life hybrid usage. If Android Enterprise capabilities draw the path of device administration, it does not however provide corporate tailored security, and this is the pitfall to be avoided when implementing it. Like any other device (Android, iOS), Android Enterprise must fall under the company security policy and benefit from real-time threat defense to ensure the protection of corporate data. Microsoft and Pradeo combine their capabilities to provide a thorough and dynamic security posture to Microsoft Endpoint Manager users and protect all the devices of the mobile fleet.
To learn more about Microsoft Security solutions visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
READ MORE HERE