Alternative ways for security professionals and IT to achieve modern security controls in today’s unique remote work scenarios

With the bulk of end users now working remotely, legacy network architectures that route all remote traffic through a central corporate network are suddenly under enormous strain. The result can be poorer performance, productivity, and user experience. Many organizations are now rethinking their network infrastructure design to address these issues, especially for applications like Microsoft Teams and Office 365. At Microsoft, for example, we adopted split tunneling as part of our VPN strategy. Our customers have asked us for guidance on how to manage security in this changing environment.
An architecture that routes all remote traffic back to the corporate network was originally intended to provide the security team with the following:
- Prevention of unauthorized access
- Control of authorized user access
- Network protections such as Intrusion Detection/Prevention (IDS/IPS) and Distributed Denial of Service (DDoS) mitigation
- Data loss prevention (DLP)
In this post, we’ll address alternative ways of achieving modern security controls, so security teams can manage risk in a more direct-to-internet network architecture.
Prevention of unauthorized access
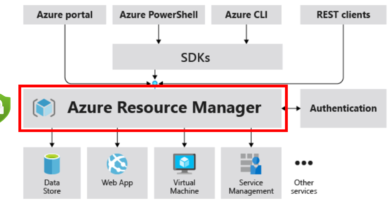
Multi-factor authentication (MFA) helps increase authentication assurance. We recommend requiring it for all users. If you are not ready to deploy to all users, consider entering an emergency pilot for higher risk or more targeted users. Learn more about how to use Azure Active Directory (Azure AD) Conditional Access to enforce MFA. You will also want to block legacy authentication protocols that allow users to bypass MFA requirements.
Control of authorized user access
Ensure only registered devices that comply with your organization’s security policies can access your environment, to reduce the risk that would be posed by resident malware or intruders. Learn more about how to use Azure AD Conditional Access to enforce device health requirements. To further increase your level of assurance, you can evaluate user and sign-on risk to block or restrict risky user access. You may also want to prevent your users from accessing other organizations’ instances of the Office 365 applications. If you do this with Azure AD tenant restrictions, only logon traffic needs to traverse the VPN.
Network protections
Some of the protections that you may have traditionally provided by routing traffic back through your corporate network can now be provided by the cloud apps your users are accessing. Office 365, for example, is globally distributed and designed to allow the customer network to route user requests to the closest Office 365 service entry point. Learn more about Office 365 network connectivity principles. We build resiliency into Office 365 to minimize potential disruption. We protect Office 365 and Azure from network attacks like DDoS on behalf of our customers.
With the above controls in place, you may be ready to route remote users’ traffic directly to Office 365. If you still require a VPN link for access to other applications, you can greatly improve your performance and user experience by implementing split tunneling.
We strongly recommend that you review VPN and VPS infrastructure for updates, as attackers are actively tailoring exploits to take advantage of remote workers. Microsoft Threat Intelligence teams have observed multiple nation state and cybercrime actors targeting unpatched VPN systems for many months. In October 2019, both the National Security Agency and National Cyber Security Centre issued alerts on these attacks. The Department of Homeland Security Cybersecurity and Infrastructure Security Agency (CISA) and Department of Commerce National Institute of Standards and Technology (NIST) have published useful guidance on securing VPN/VPS infrastructure.
DLP
To help you prevent the accidental disclosure of sensitive information, Office 365 has a rich set of built-in tools. You can use the built-in DLP capabilities of Teams and SharePoint to detect inappropriately stored or shared sensitive information. If part of your remote work strategy involves a bring-your-own-device (BYOD) policy, you can use Conditional Access App Control to prevent sensitive data from being downloaded to users’ personal devices.
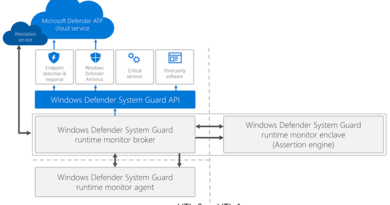
Malware detection
By default, SharePoint Online automatically scans file uploads for known malware. Enable Exchange Online Protection to scan email messages for malware. If your Office 365 subscription includes Office 365 Advanced Threat Protection (ATP), enable it to provide advanced protection against malware. If your organization uses Microsoft Defender ATP for endpoint protection, remember that each user is licensed for up to five company-managed devices.
Additional resources
READ MORE HERE