Addressing cybersecurity risk in industrial IoT and OT
As the industrial Internet of Things (IIoT) and operational technology (OT) continue to evolve and grow, so too, do the responsibilities of the Chief Information Security Officer (CISO). The CISO now needs to mitigate risks from cloud-connected machinery, warehouse systems, and smart devices scattered among hundreds of workstations. Managing those security risks includes the need to ensure safety in manufacturing, oil and gas facilities, public utilities, transportation, civic infrastructure, and more.
Analysts predict that we’ll have roughly 21.5 billion IoT devices connected worldwide in 2025, drastically increasing the surface area for attacks. Because embedded devices often go unpatched, CISO’s need new strategies to mitigate IIoT/OT risks that differ in crucial ways from those found in information technology (IT). The difference needs to be understood by your Board of Directors (BoD) and leadership team. Costly production outages, safety failures with injuries or loss of life, environmental damage leading to liability—all are potentially disastrous scenarios that have moved IIoT and OT to the center of cyber threat management.
An evolving threat landscape
Both IIoT and OT are considered cyber-physical systems (CPS); meaning, they encompass both the digital and physical worlds. This makes any CPS a desirable target for adversaries seeking to cause environmental contamination or operational disruption. As recent history shows, such attacks are already underway. Examples include the TRITON attack—intended to cause a serious safety incident—on a Middle East chemical facility and the Ukrainian electrical-grid attacks. In 2017, ransomware dubbed NotPetya paralyzed the mighty Maersk shipping line and nearly halted close to a fifth of the world’s shipping capacity. It also spread to pharma giant Merck, FedEx, and numerous European firms before boomeranging back to Russia to attack the state oil company, Rosneft.
In 2019, Microsoft observed a Russian state-sponsored attack using IoT smart devices—a VOIP phone, an office printer, and a video decoder—as entry points into corporate networks, from which they attempted to elevate privileges. Attackers have even compromised building access control systems to move into corporate networks using distributed denial-of-service (DDoS) attacks; wherein, a computer system is overwhelmed and crashed with an onslaught of traffic.
The current model
Since the 1990’s, the Purdue Enterprise Reference Architecture (PERA), aka the Purdue Model, has been the standard model for organizing (and segregating) enterprise and industrial control system (ICS) network functions. PERA divides the enterprise into various “Levels,” with each representing a subset of systems. Security controls between each level are typified by a “demilitarized zone” (DMZ) and a firewall.
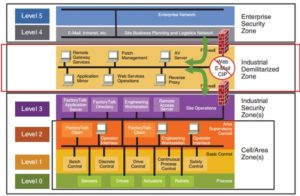
Conventional approaches restrict downward access to Level 3 from Levels 4, 5 (and the internet). Heading upward, only Layer 2 or 3 can communicate with Layers 4 and 5, and the lowest two Levels (machinery and process) must keep their data and communications within the organization’s OT.
But in our IIoT era, data no longer flows in a hierarchical fashion as prescribed by the Purdue Model. With the rise of edge computing, smart sensors, and controllers (Levels O, 1) now bypass firewalls and communicate directly with the cloud, creating new risks for system exposure.
Modernizing this model with Zero Trust principles at Levels 4 and 5 can help bring an organization’s IIoT/OT into full compliance for the cloud era.
A new strategy
Consequence-driven cyber-informed engineering (CCE) is a new methodology designed by Idaho National Labs (INL) to address the unique risks posed by IIoT/OT. Unlike conventual approaches to cybersecurity, CCE views consequence as the first aspect of risk management and proactively engineers for potential impacts. Based on CCE, there are four steps that your organization—public or private—should prioritize:
- Identify your “crown jewel” processes: Concentrate on protecting critical “must-not-fail” functions whose failure could cause safety, operational, or environmental damage.
- Map your digital estate: Examine all the digital pathways that could be exploited by adversaries. Identify all of your connected assets—IT, IoT, building management systems (BMS), OT, smart personal devices—and understand who has access to what, including vendors, maintenance people, and remote workers.
- Spotlight likely attack paths: Analyze vulnerabilities to determine attack routes leading to your crown jewel processes, including possible social engineering schemes and physical access to your facilities.
- Mitigate and protect: Prioritize options that allow you to “engineer out” cyber risks that present the highest consequences. Implement Zero Trust segmentation policies to separate IIoT and OT devices from other networks. Reduce the number of internet-accessible entry points and patch vulnerabilities in likely attack paths.
Making the case in real terms
Your leadership and BoD have a vested interest in seeing a return on investment (ROI) for any new software or hardware. Usually, the type of ROI they want and expect is increased revenue. But returns on security software often can’t be seen in a quarterly statement. That means cybersecurity professionals have to present a solid case. Here are some straightforward benefits to investing in IIoT/OT cybersecurity software that you can take into the boardroom:
- Prevent safety or environmental costs: Security failures at chemical, mining, oil, transportation, or other industrial facilities can cause consequences more dire than an IT breach. Lives can be lost, and costs incurred from toxic clean-up, legal liability, and brand damage can reach into the hundreds of millions.
- Minimize downtime: As the NotPetya and LockerGoga attacks demonstrated, downtime incurs real financial losses that affect everyone—from plant personnel all the way up to shareholders.
- Stop IP theft: Companies in the pharmaceutical industry, energy production, defense, high-tech, and others spend millions on research and development. Losses from having their intellectual property stolen by nation states or competitors can also be measured in the millions.
- Avoid regulatory fines: Industries such as pharmaceuticals, oil/gas, transportation, and healthcare are heavily regulated. Therefore, they are vulnerable to large fines if a security breach in IIoT/OT causes environmental damage or loss of life.
The way forward
For today’s CISO, securing the digital estate now means being accountable for all digital security—IT, OT, IIoT, BMS, and more. This requires an integrated approach—embracing people, processes, and technology. A good checklist to start with includes:
- Enable IT and OT teams to embrace their common goal—supporting the organization.
- Bring your IT security people onsite so they can understand how OT processes function.
- Show OT personnel how visibility helps the cybersecurity team increase safety and efficiency.
- Bring OT and IT together to find shared solutions.
With attackers now pivoting across both IT and OT environments, Microsoft developed Azure Defender for IoT to integrate seamlessly with Azure Sentinel and Azure Sphere—making it easy to track threats across your entire enterprise. Azure Defender for IoT utilizes:
- Automated asset discovery for both new greenfield and legacy unmanaged IoT/OT devices.
- Vulnerability management to identify IIoT/OT risks, detect unauthorized changes, and prioritize mitigation.
- IIoT/OT-aware behavioral analytics to detect advanced threats faster and more accurately.
- Integration with Azure Sentinel and third-party solutions like other SIEMs, ticketing, and CMDBs.
Azure Defender for IoT makes it easier to see and mitigate risks and present those risks to your BoD. Microsoft invests more than USD1 billion annually on cybersecurity research, which is why Azure has more compliance certifications than any other cloud provider.
Plain language and concrete examples go far when making the case for IIoT/OT security software. Your organization should define what it will—and more importantly, will not—tolerate as operational risks. For example: “We tolerate no risk to human life or safety”; “no permanent damage to the ecosystem”; “no downtime that will cost jobs.” Given the potential for damages incurred from downtime, injuries, environmental liability, or tarnishing your brand, an investment in cybersecurity software for IIoT/OT makes both financial and ethical sense.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
READ MORE HERE