A Peek Into CISA’s Post-Quantum Cryptography Roadmap
Practically speaking, quantum computers are still years away, but the US Cybersecurity and Infrastructure Agency is still recommending that organizations begin preparations for the migration to the post-quantum cryptographic standard.
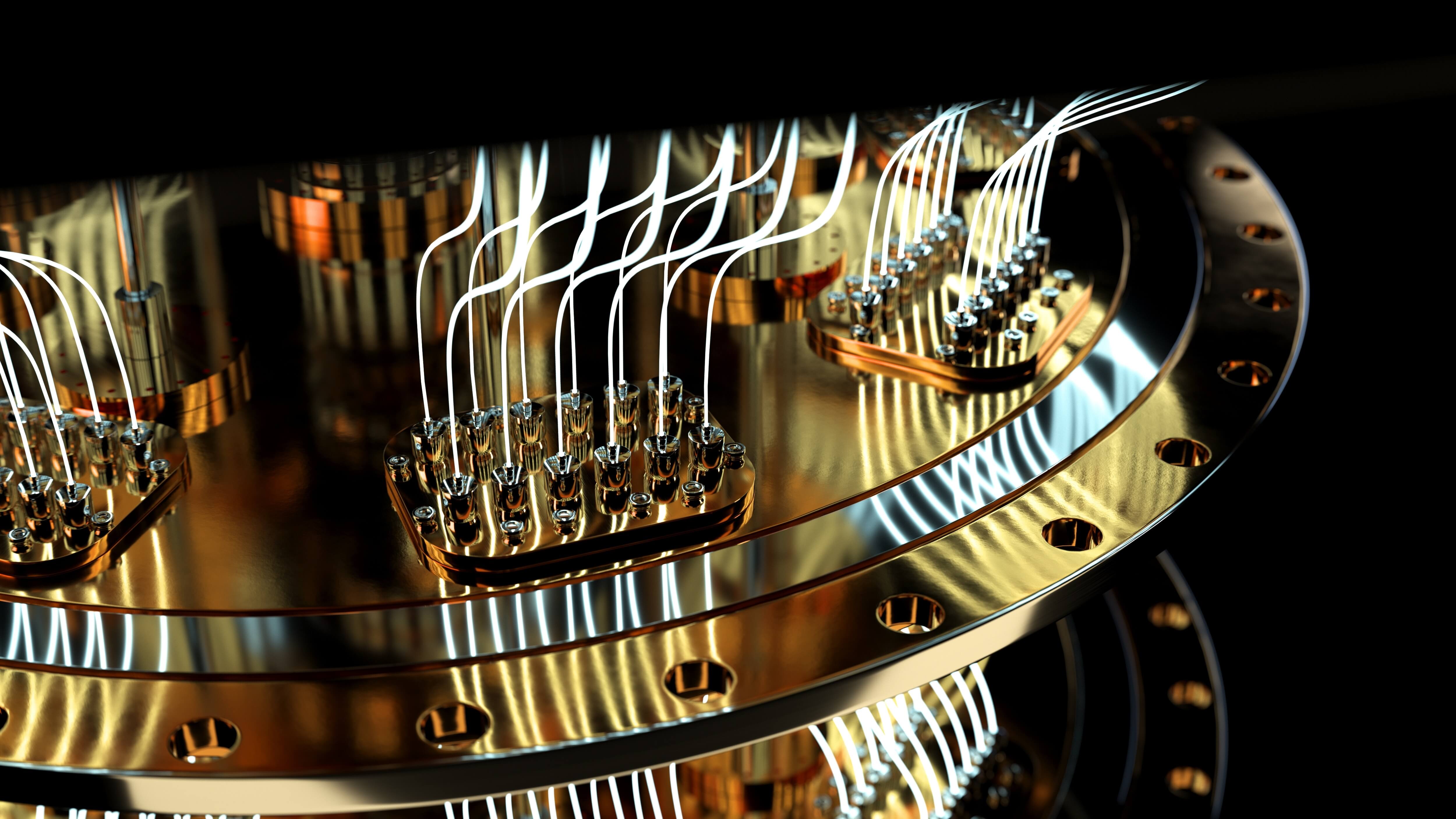
Quantum computers use quantum bits (qubits) to deliver higher computing power and speed, and are expected to be capable of breaking existing cryptographic algorithms, such as RSA and elliptic curve cryptography. This would impact the security of all online communications as well as data confidentiality and integrity. Security experts have warned that practical quantum computers could be less than a decade away.
The National Institute of Standards and Technology announced the first four quantum-resistant algorithms that will become part of the post-quantum-cryptographic standard in July, but the final standard is not expected until 2024. Even so, CISA is encouraging critical infrastructure operators to begin their preparations in advance.
“While quantum computing technology capable of breaking public key encryption algorithms in the current standards does not yet exist, government and critical infrastructure entities—including both public and private organizations—must work together to prepare for a new post-quantum cryptographic standard to defend against future threats,” CISA says.
To help organizations with their plans, NIST and the Department of Homeland Security developed the Post-Quantum Cryptography Roadmap. The first step should be creating an inventory of vulnerable critical infrastructure systems, CISA said.
Organizations should identify where, and for what purpose, public key cryptography is being used, and mark those systems as quantum-vulnerable. This includes creating an inventory of the most sensitive and critical datasets that must be secured for an extended amount of time, and all systems using cryptographic technologies. Having a list of all the systems would ease the transition when it comes times to make the switch.
Read More HERE

