4 tried-and-true prevention strategies for enterprise-level security

Why is it that dentists advise people over and over to floss, yet so few do it? It only takes a minute of your time, yet if you’re running late or feeling tired, you may be tempted to skip it. That is until you remember your upcoming teeth cleaning appointment. There is nothing like the memory of a long and painful visit to the dentist to motivate good dental hygiene. Smart habits today can save you time and money later.
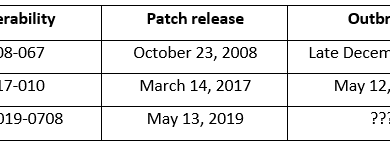
Good habits are also important in cybersecurity. It is typically much cheaper to prevent an attack than to respond to one already in motion. A great example is the WannaCry ransomware attack. Attackers exploited a vulnerability, which resulted in as much as $4 billion worth of damage around the world. The vulnerability had been patched in a security update released by Microsoft one month prior to the attack, so organizations who had installed the latest updates were spared.
Sometimes cyber hygiene advice is ignored because it’s not the new, shiny whiz-bang solution du jour. It’s easier to get attention for a sparkly light-up electric toothbrush than for a plain old piece of dental floss, but that “plain old” floss is key to keeping your choppers cavity free.
With this in mind, we broke out the four best practices of cyber hygiene, outlined in 24th edition of the Microsoft Security Intelligence Report (SIR), to help reduce your risk of attack:
- Practice good security hygiene.
- Implement access tiers among employees.
- Always back up important data.
- Teach employees how to spot and report suspicious activity.
Practice good security hygiene
Good security hygiene includes routine policies and procedures to maintain and protect your IT systems and devices:
- Use only trusted software—If you can’t validate the credibility of the vendor or supplier, don’t use it. Avoid free software from an unknown source.
- Deploy software updates—Keep your software and operating systems up to date. Vendors regularly release security updates to their applications, and the only way you can take advantage of this is if you deploy the updates. You should also be sure to apply the security configuration baselines provided by your software vendors.
- Protect email and browsers—Attackers frequently conduct social engineering attacks through email and browsers, so it’s important to deploy security updates as soon as they are available. And deploy advanced threat protection capabilities for your email, browser, and email gateway to help safeguard your organization from modern phishing variants.
Implement access tiers among employees
The principle of least privilege should guide your access control policies. Malicious actors want to take control of the most privileged accounts in your organization, so the fewer people that have them the better. You also should be mindful that even though your company may have a “trusted software only” mandate, employees may unwittingly download unsafe software that can spread “malcode” throughout your organization.
- Give system access on a need-to-know basis—Set up role-based access to easily onboard users to the systems they need to do their jobs and nothing more. Keep administrative accounts separate from information worker accounts, so that users only sign in to administrative accounts when they need them. Set up just-in-time privileges that give users with administrative accounts access to systems only when they need them and for a limited time.
- Don’t allow users to download applications from anywhere but an app store—Deploy strong code integrity policies, including restricting the applications that users can run with whitelisting. If possible, adopt a security solution to restrict the code that runs in the system core (kernel) and can block unsigned scripts and other forms of untrusted code.
Always back up important data
Your organization’s data is often its most valuable asset. If you suffer a security breach or a ransomware attack, a good backup process can save you if your data is destroyed or removed.
- Back up data online—Use cloud storage services for automatic backup of data online.
- Use the 3-2-1 method for your most important data—For on-premises data, keep three backups of your data, on two different storage types, and at least one backup offsite.
Teach employees how to spot and report suspicious activity
Your employees are a constant target of attackers, and many are tricked into downloading malicious software or sharing their credentials. They can also be your first line of defense. A strong cybersecurity education program can turn employees from targets to first responders.
- Recognize social engineering and spear-phishing attacks—Attackers continuously update the methods they use to gain employee trust and access. Provide context about how these attacks work, including the latest techniques and relevant examples.
- Use your web browser safely—Educate employees about the dangers of unsafe websites, such as cryptocurrency mining. Ensure they keep their browsers up to date with the latest security features and solutions that provide warnings about unsafe sites.
- Identify suspicious file types—Teach employees to look for suspicious files if a computer is running exceptionally slow and encourage them to submit a sample to the operating system vendor.
- Engage IT if you’re not sure about something—Make sure that employees know how to report suspicious communications or get advice from IT on what to do about it.
Learn more
There’s probably nothing that surprised you on this list, but can you confirm with 100 percent certainty that your company is practicing and enforcing all of these cyber hygiene recommendations? Instituting security preventative practices may not be as easy as flossing your teeth, but there are resources that can help.
For more details about these and other security recommendations:
READ MORE HERE