3 Major Benefits of Cloud Migration: Automation Cloud Security Specialist

Workload Security
Learn more about how automated security controls, policies, and scans can simplify security.
Related articles in the Cloud Migration series:
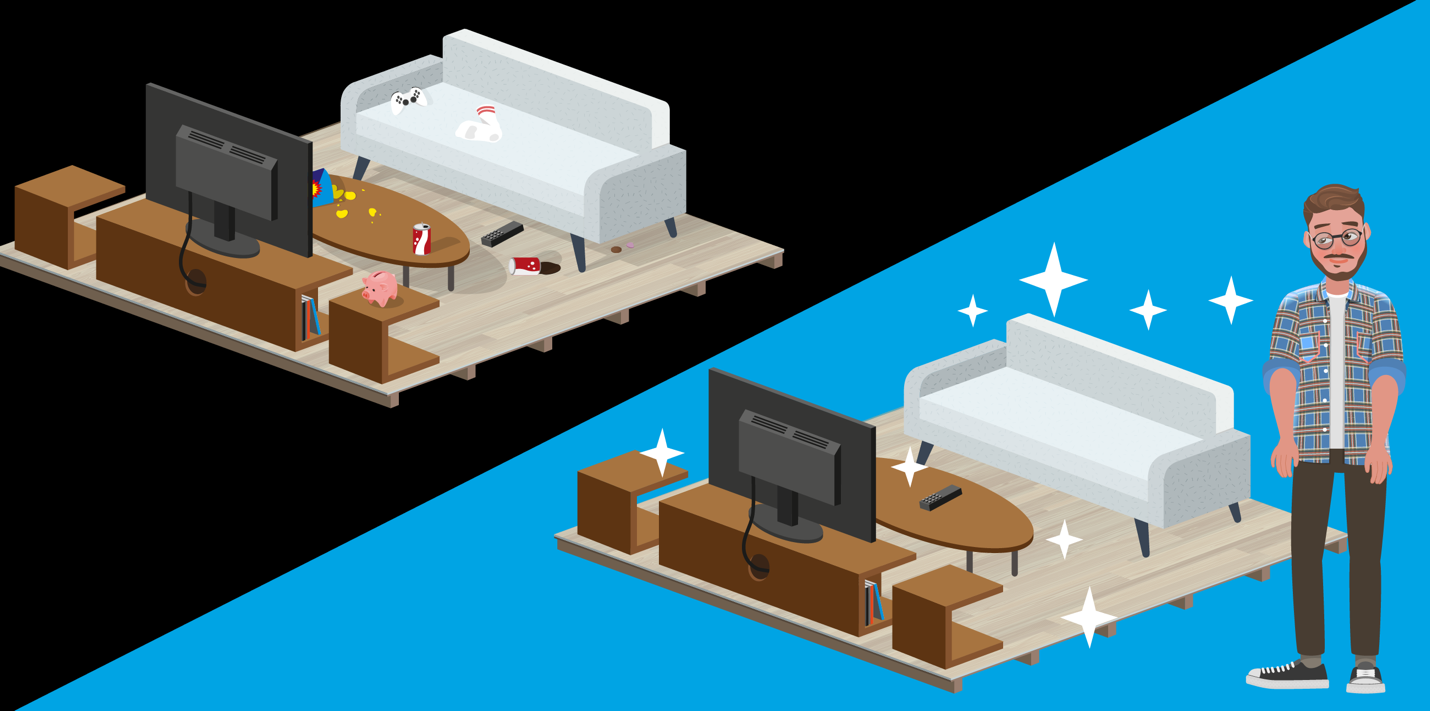
Automation is the bedrock to innovation, allowing people to work smarter not harder. Think of major inventions like the dishwasher, laundry machines, and the robotic vacuum. All of these automate processes that are mundane, tedious, and time-consuming on their own. In the cloud, automation simplifies security, allowing you to shift your focus from manually deploying security for new infrastructure, reconfiguring or remediating risks to better investigation and other security business transformation projects.
The importance of automation is reflected by its demand from security leaders. According to a study by Fegue, 95% of the IT, cloud, and security professionals surveyed said that security automation would enable them to be more efficient and make cloud-based data security more effective.
Let’s dive into the benefits of security automation, specific use cases, and how to select the right tool for your cloud migration journey:

Benefits of cloud security automation Besides the obvious point that automation simplifies security by eliminating manual tasks, freeing you to focus on innovating, here’s how automation can help you get ahead:
- Minimizes misconfigurations: Human error remains the #1 cause of cloud misconfigurations. Automation eliminates the guesswork and human errors that can compromise your infrastructure.
- More resilience: Just like you wouldn’t go without home insurance, having a back-up process is essential. By automating that process, you minimize recovery time and can limit the impacts of a breach.
- Fosters a DevSecOps culture by shifting left: Ensure security from the very beginning of the build process throughout deployment by integrating automated scans and testing from the moment code is committed to the repository.
- Accelerates compliance: Performing manual compliance audits is a no-go when DevOps teams need to be as agile as possible. By automating compliance scans continuously and security policies throughout the development process, you can make sure you’re demonstrating compliance without compromising build time.

Automation use cases
There’s a lot of ways you can incorporate automation into your cloud migration journey—so where should you start? Here are a couple suggestions:
Manage permissions
Securing user permissions is the first line of defense against data breaches, like how locked doors and windows are against potential burglaries. Manually authorizing, tracking, and deprovisioning access can be difficult considering the sheer amount of cloud resources you have. Automation tools can streamline this process by allowing you to create permissions based on roles, enabling multi-factor authentication (MFA), and requiring regular password rotation. Automation can also identify overly permissive user and service accounts.
Infrastructure as code
Think of using infrastructure as code (IaC) like building a home yourself (with no knowledge) versus using a reliable home builder. You could learn along the way and hopefully build something secure, but this will waste a lot of time, resources, and money. A builder comes in with a plan and the resources to lay a strong foundation for your house to be built upon. Similarly, IaC quickly establishes the strong foundation for developers to build upon, instead of the time-consuming alternative of manually building and configuring the infrastructure.
Virtual patching
There’s no such thing as being 100% secure, so in the off chance something does slip through the cracks, you need automated identification and remediation to limit the impact and remain compliant. Virtual patching can be automatically applied to known and unknown vulnerabilities on affected servers and endpoints before the vendor patch is released. This saves you countless hours and potential system downtime from trying to manually locate and patch everything yourself.
Choose your fighter: Automation tools

As we’ve reiterated throughout this series, a cybersecurity platform solution is ideal, but they’re not all equal. Your tool of choice should be able to handle the specific use cases we listed (permissions, IaC, and remediation) as well as:
- Discovery of workloads and cloud infrastructure across all the major cloud service providers (CSPs), including Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform™.
- Continuous scanning and monitoring of IaC templates, instances, applications, cloud file storage, cloud networks, and everything in between for vulnerabilities, malware, and compliance risks. Yes, we already mentioned compliance scanning in this article, but it’s so important it needs to be said twice (at least). Automated scanning should also generate reports, logs, and alerts, so you can stay on top of anything unusual.
- Detection and remediation of known and unknown vulnerabilities or risks to minimize disruption to workflows.
- Integration with your existing tool set for automated security deployment, policy configuration and management, health checks, incident response, and more.
Next steps
Automation is the key to migrating to the cloud smoothly and efficiently. Think of automation like the power to your home. Your dishwasher, laundry machines, and robotic vacuums can’t work without power—therefore rendering them useless. After you’ve put your security strategy together, incorporating automation allows it to go from paper to practice.
Trend Micro Cloud One™ is a security services platform compromised of seven solutions. Each solution is purpose-built for cloud builders to simplify their security approach while providing cutting-edge protection. Here’s a look at how our solutions check all the boxes:
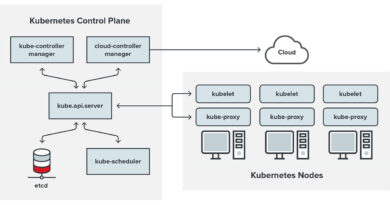
- Discovery of workloads and cloud infrastructure: Trend Micro Cloud One™ – Workload Security is optimized for DevOps thanks to strong API integration with Microsoft Azure, AWS, and Google Cloud. Workload Security automatically protects new and existing workloads across your mixed environment of virtual, physical, cloud, and containers.
- Continuous scanning and monitoring:
- Trend Micro Cloud One™ – Conformity provides continuous security, compliance, and governance checks against nearly 1,000 configuration best practices and nearly 100 services from major CSPs. Check IaC templates thanks to CloudFormation Template Scanning and run preconfigured or customized reports with an endless combination of filters.
- Trend Micro Cloud One™ – File Storage Security provides automated malware scanning whenever new files are uploaded to block known bad files and protect against malware variants. By scanning files of all sizes and types, DevOps teams workflows remain uninterrupted and secure.
- Detection and remediation: Trend Micro Cloud One™ – Network Security deploys without disruption or need to rearchitect and immediately inspects ingress and egress traffic. It also includes virtual patching and post-compromise detection and disruption, so you’re secured against all phases of the attack life cycle.
- Integration with your existing tool set: Thanks to powerful APIs, all seven solutions integrate seamlessly with your favorite communication, deployment, orchestration, cloud storage, and other tools from major CSPs.
- Managing permissions: Conformity automatically ensures your AWS Identity Access and Management (IAM) policies are enforced thanks to many IAM configuration checks.
- Infrastructure as a code: Conformity ensures your IaC templates are secure and compliant via automated scans against industry best practices.
Simplify your cloud migration journey by experiencing the benefits of automation with a free 30-day trial of Trend Micro Cloud One.
- Trend Micro Cloud One™ – Workload Security: Runtime protection for virtual, physical, cloud, and container workloads
- Trend Micro Cloud One™ – Container Security: Automated image scanning in your build pipeline
- Trend Micro Cloud One™ – File Storage Security: Security for cloud file and object storage services
- Trend Micro Cloud One™ – Application Security: Security for serverless functions, APIs, and applications
- Trend Micro Cloud One™ – Network Security: Cloud network layer intrusion protection system (IPS) security
- Trend Micro Cloud One™ – Conformity: Cloud security and compliance posture management
- NEW – Trend Micro Cloud One™ – Open Source Security by Snyk: Visibility and monitoring of open source vulnerabilities and license risks
Tags
sXpIBdPeKzI9PC2p0SWMpUSM2NSxWzPyXTMLlbXmYa0R20xk
Read More HERE