ViperSoftX Updates Encryption, Steals Data
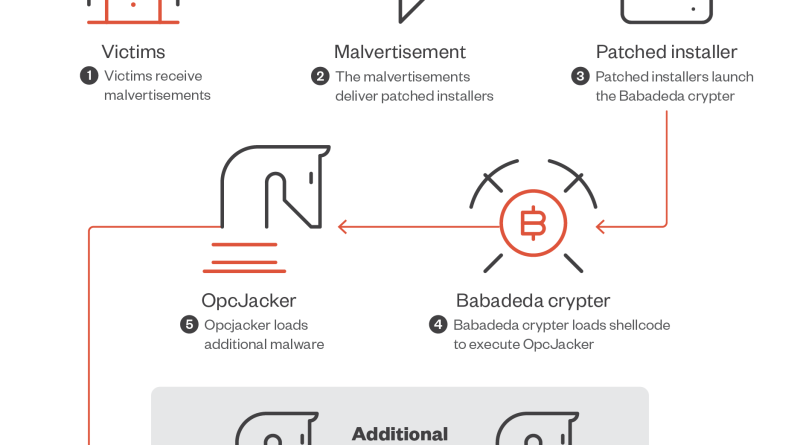
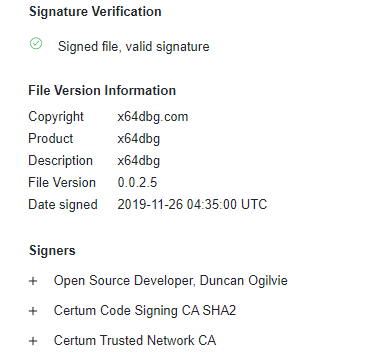
We observed cryptocurrency and information stealer ViperSoftX evading initial loader detection and making its lure more believable by making the initial package loader via cracks, keygens, activators, and packers non-malicious. We also noted more sophisticated encryption and basic anti-analysis techniques, such as byte remapping and web browser communication blocking. Read More HERE…