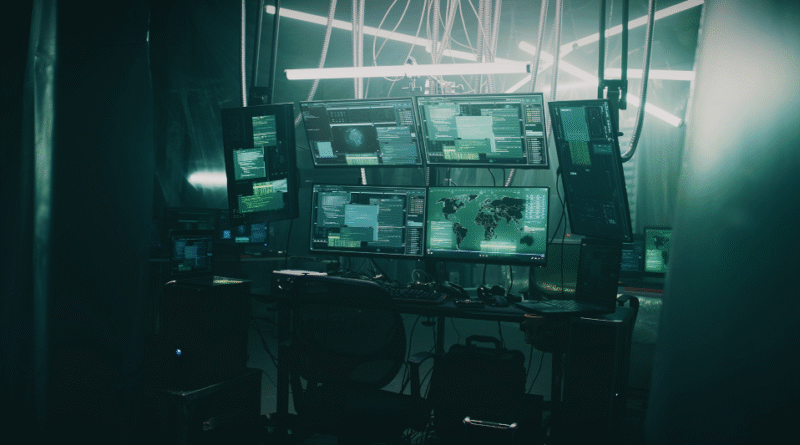
Inside SHADOW-WATER-063’s Banana RAT: From Build Server to Banking Fraud
In this blog entry, researchers from the TrendAI™ MDR team discuss how they mapped the full end-to-end operation of SHADOW-WATER-063’s Banana RAT banking malware by analyzing server-side artifacts and victim-side data. Read More HERE…