Structured threat hunting: One way Microsoft Threat Experts prioritizes customer defense
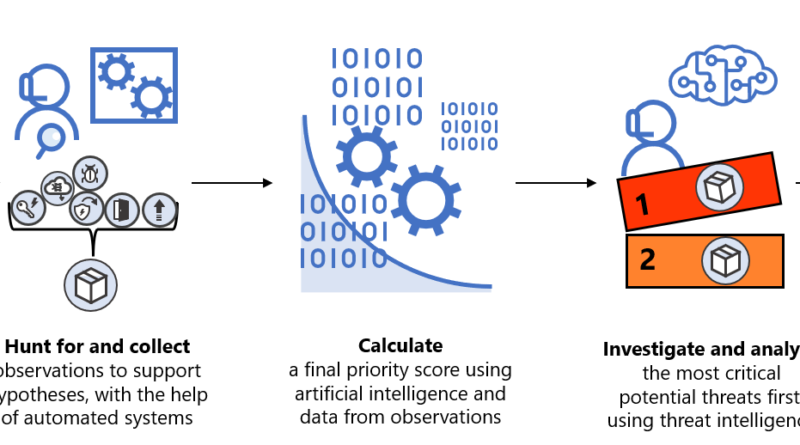
Our approach to threat hunting is designed to evaluate impact and escalate potential threats for investigation, based on how damaging the potential threat would be. It is also designed for speed: due to the highly time-sensitive nature of the threat response, the most dangerous potential threats are analyzed first.
The post Structured threat hunting: One way Microsoft Threat Experts prioritizes customer defense appeared first on Microsoft Security Blog. READ MORE HERE…